Secure the Future: Crafting Resilient Code as a Cybersecurity Programmer
In the US job market, recruiters spend seconds scanning a resume. They look for impact (metrics), clear tech or domain skills, and education. This guide helps you build an ATS-friendly Cybersecurity Programmer resume that passes filters used by top US companies. Use US Letter size, one page for under 10 years experience, and no photo.
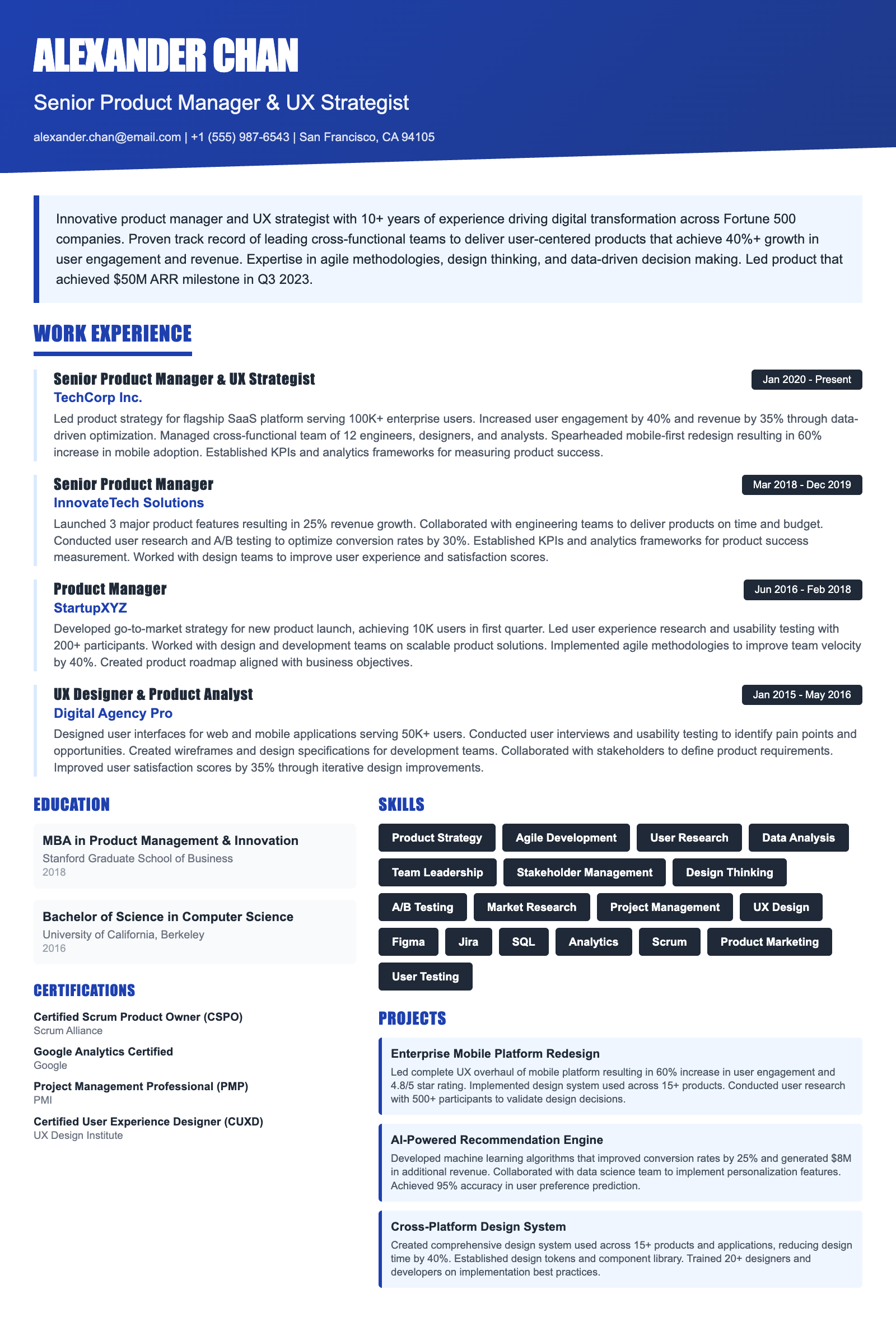
Expert Tip: For Cybersecurity Programmer positions in the US, recruiters increasingly look for technical execution and adaptability over simple job duties. This guide is tailored to highlight these specific traits to ensure your resume stands out in the competitive Cybersecurity Programmer sector.
What US Hiring Managers Look For in a Cybersecurity Programmer Resume
When reviewing Cybersecurity Programmer candidates, recruiters and hiring managers in the US focus on a few critical areas. Making these elements clear and easy to find on your resume will improve your chances of moving to the interview stage.
- Relevant experience and impact in Cybersecurity Programmer or closely related roles.
- Clear, measurable achievements (metrics, scope, outcomes) rather than duties.
- Skills and keywords that match the job description and ATS requirements.
- Professional formatting and no spelling or grammar errors.
- Consistency between your resume, LinkedIn, and application.
Essential Skills for Cybersecurity Programmer
Include these keywords in your resume to pass ATS screening and impress recruiters.
- Relevant experience and impact in Cybersecurity Programmer or closely related roles.
- Clear, measurable achievements (metrics, scope, outcomes) rather than duties.
- Skills and keywords that match the job description and ATS requirements.
- Professional formatting and no spelling or grammar errors.
- Consistency between your resume, LinkedIn, and application.
A Day in the Life
My day often starts with threat intelligence reports, analyzing emerging vulnerabilities, and adapting security protocols accordingly. A significant portion involves writing and testing secure code for applications, ensuring adherence to industry best practices like OWASP. Daily tasks include penetration testing and vulnerability assessments using tools like Metasploit and Nmap. Collaboration is key, participating in stand-up meetings with security engineers and developers to discuss progress and challenges. Incident response is a priority, addressing security breaches by analyzing logs with Splunk and implementing immediate containment measures. Deliverables could range from detailed vulnerability reports to patched application code, contributing to a stronger security posture for the organization.
Career Progression Path
Entry-level or junior Cybersecurity Programmer roles (building foundational skills).
Mid-level Cybersecurity Programmer (independent ownership and cross-team work).
Senior or lead Cybersecurity Programmer (mentorship and larger scope).
Principal, manager, or director (strategy and team/org impact).
Interview Questions & Answers
Prepare for your Cybersecurity Programmer interview with these commonly asked questions.
Describe a time when you identified and mitigated a significant security vulnerability in a software application.
MediumExplain the difference between symmetric and asymmetric encryption. Provide examples of when each would be used.
MediumHow would you approach securing a new cloud-based application?
HardWhat are some common web application security vulnerabilities, and how can they be prevented?
MediumDescribe your experience with incident response. What steps would you take if you detected a security breach?
MediumImagine you're tasked with improving the security of a legacy application with known vulnerabilities. How would you prioritize your efforts?
HardATS Optimization Tips
Make sure your resume passes Applicant Tracking Systems used by US employers.
Common Resume Mistakes to Avoid
Don't make these errors that get resumes rejected.
Industry Outlook
Top Hiring Companies
Frequently Asked Questions
What is the ideal resume length for a Cybersecurity Programmer?
What key skills should I emphasize on my Cybersecurity Programmer resume?
How can I ensure my Cybersecurity Programmer resume is ATS-friendly?
Should I include cybersecurity certifications on my resume?
What are some common mistakes to avoid on a Cybersecurity Programmer resume?
How do I transition to a Cybersecurity Programmer role from a different field?
Continue Your Cybersecurity Programmer Career Research
Ready to Build Your Cybersecurity Programmer Resume?
Use our AI-powered resume builder to create an ATS-optimized resume tailored for Cybersecurity Programmer positions in the US market.
Complete Cybersecurity Programmer Career Toolkit
Everything you need for your Cybersecurity Programmer job search — all in one platform.
Cybersecurity Programmer Interview Questions
Practice with 20+ curated questions
Cybersecurity Programmer Salary Guide
Salary ranges, negotiation tips, market data
ATS Resume Checker
Check if your resume passes ATS filters
AI Mock Interview
Practice with AI feedback and scoring
Why choose ResumeGyani over Zety or Resume.io?
The only platform with AI mock interviews + resume builder + job search + career coaching — all in one.
Last updated: March 2026 · Content reviewed by certified resume writers · Optimized for US job market